Auth0
Add Auth0 OpenID Connect for your marketplace
Overview
This article provides step-by-step instructions for setting up a new Auth0 tenant and application, as well as configuring OIDC (OpenID Connect) authentication in Gigantik CMS using Auth0 as the identity provider. OIDC authentication allows collectors to securely authenticate and access your Gigantik Marketplace using their existing Auth0 accounts.
Prerequisites
Before proceeding, ensure that you have the following:
- A valid Auth0 account
- Access to the Gigantik CMS
Creating a New Auth0 Tenant
To create a new Auth0 tenant, follow these steps:
- Log in to your Auth0 account.
- Navigate to the Auth0 Dashboard.
- Click on your tenant name in the top-left drop-down menu.
- Click on the Create Tenant button.
- Provide a name, the hosted region, and the environment tag for your new tenant.
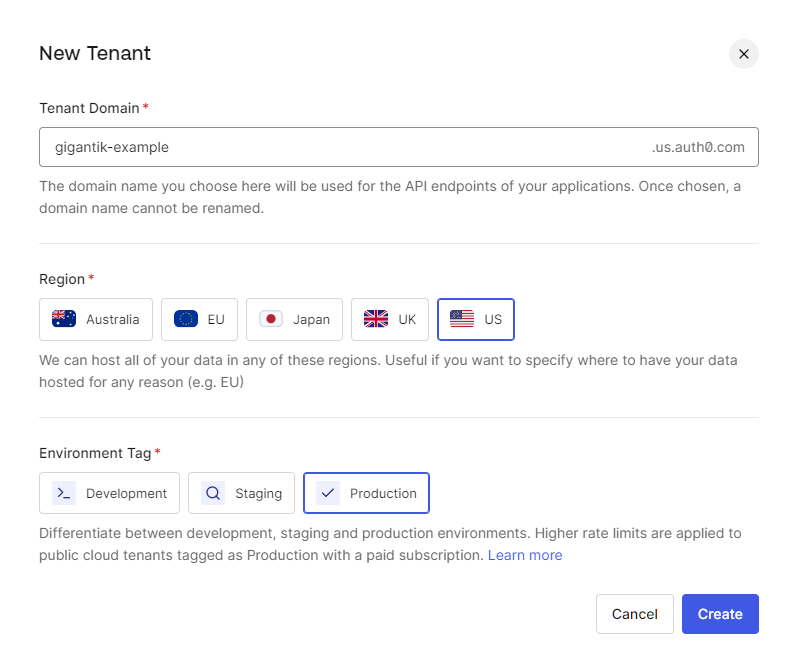
An Example Tenant
- Click Create.
This process may change based on decisions at Auth0. Please see the official documentation:
https://auth0.com/docs/get-started/auth0-overview/create-tenants
Creating a new Application in Auth0
To create a new application in Auth0 or use the default application, use the following instructions:
- Log in to the Auth0 Dashboard.
- Select the desired tenant from the "Tenants" drop-down menu.
- Click on Applications >Applications in the left-hand menu.
- Click on the Create Application button.
- Enter a name for your application.
- Choose Single Page Web App as the application type.
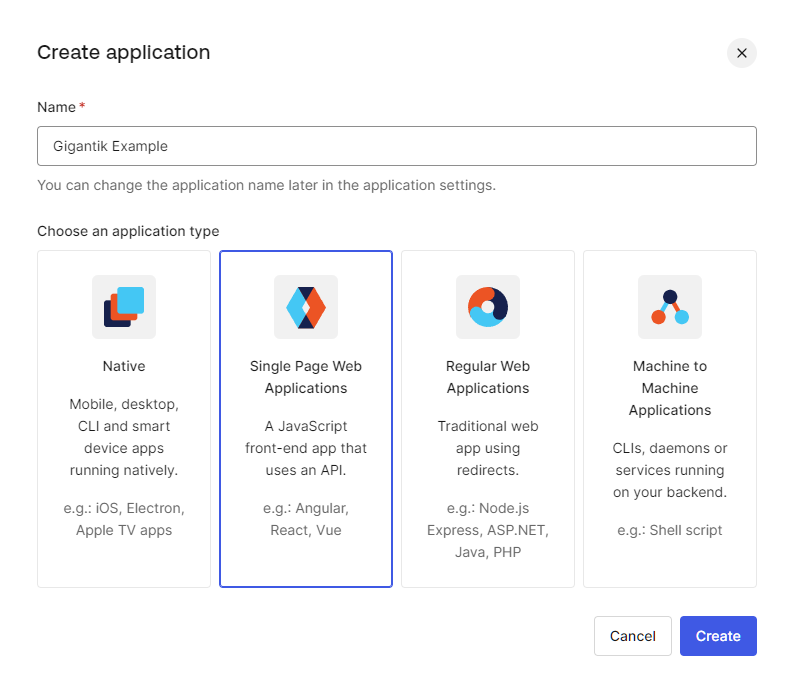
Selecting Single Page Web Applications
- Click Create.
Configuring Application Settings
To configure the application settings in Auth0, follow these steps:
- In the Applications dashboard, click on your newly created application.
- Select the Settings tab.
- Make note of the Domain and Client ID values displayed on this page.
- Under Application URIs > Allowed Callback URLs, enter the root of your marketplace URL, including a trailing slash. For example, enter "https://example.shops.gigantik.io/"
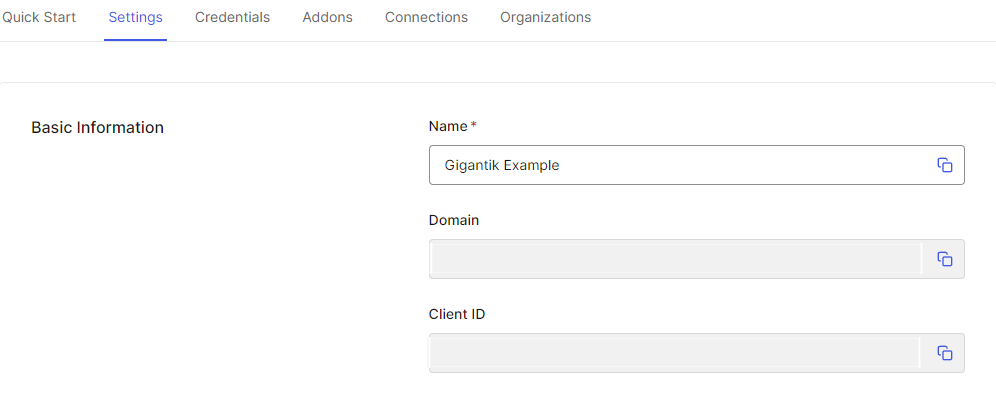
Domain and Client ID in the Auth0 Application Settings
- Click Add to Save the settings.
Configuring the OIDC Provider in the Gigantik CMS
To create an OIDC provider in Gigantik CMS and configure it with Auth0, use the following instructions:
- Log in to the Gigantik CMS
- Navigate to Marketplace > OpenID Connect
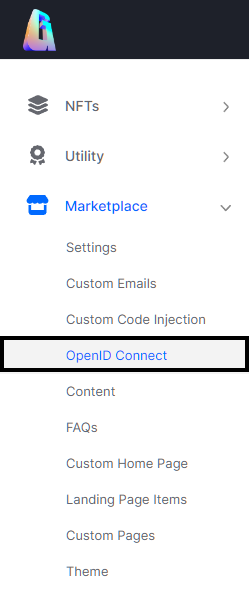
The OpenID Connect Integration in the CMS
- At the top right of the Open ID Connect screen, click the Add OpenID Connect Provider button
- Provide a name for the OIDC provider (e.g. "Auth0").
- For the Discovery Endpoint, enter the following URL, replacing with your actual Auth0 domain: https:///.well-known/openid-configuration/
- In the Client ID field, enter the client ID obtained from the Auth0 application settings (Step 2 of Configuring Application Settings).
- Optionally, you can provide a button image for the OIDC provider.
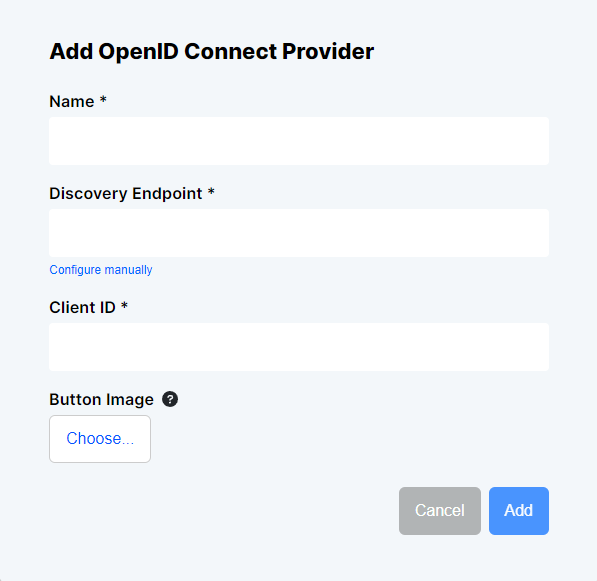
OpenID Setup in the CMS
- Save the OIDC provider configuration.
Conclusion
By following the steps outlined in this article, you should now have successfully set up OIDC authentication for your Gigantik Marketplace using Auth0 as the identity provider. With this setup, collectors can now authenticate securely and access your Gigantik marketplace using their Auth0 credentials.
For further information about advanced configuration options, refer to the official Auth0 documentation.
Updated over 1 year ago